-
FAQs
-
Sysrisk User Manual
-
- Step-by-Step Guide to SysRisk Purchasing Process
- Team or Enterprise License Purchase: Login and Profile Setting Process
- Password Management Process
- Company Profile in SysRisk
- User Creation and Role Assignment in SysRisk
- Customization and Dashboard Configuration
- Homepage Overview
- SysRisk Activity Logs
- Category Management for ERM
- Risk Approval Overview1
- Risk Entry Page for ERM
- Risk Entry Page for PRM
- Creating AI-Generated Risk Entries in SysRisk
- Risk Register Risk Prioritization Page Overview
- Risk Creation, Edit and Approval Process in SysRisk
- Risk Closure Process in SysRisk
- SysRisk Auditing Record Maintenance
- Risk Notification Settings
- Show Remaining Articles (3) Collapse Articles
-
-
Risk Management
-
- Control Risk
- ERM
- Inherent Risk
- Qualitative Risk Analysis
- Quantitative Risk Analysis
- Residual Risk
- Risk Acceptance
- Risk Acceptance Criteria
- Risk Aggregation
- Risk Analysis
- Risk Analysis Methods
- Risk Analytics
- Risk Appetite
- Risk Appetite Framework
- Risk Appetite Statement
- Risk Assessment
- Risk Assessment Matrix
- Risk Assessment Process
- Risk Attribution
- Risk Avoidance
- Risk Bearing Capacity
- Risk Benchmarking
- Risk Capacity
- Risk Capital
- Risk Clustering
- Risk Communication
- Risk Communication Plan
- Risk Concentration
- Risk Contingency
- Risk Contingency Plan
- Risk Control
- Risk Convergence
- Risk Criteria
- Risk Culture
- Risk Dashboard
- Risk Dependency
- Risk Diversification
- Risk Escalation
- Risk Escalation Path
- Risk Evaluation
- Risk Exposure
- Risk Financing
- Risk Framework
- Risk Governance
- Risk Heat Map
- Risk Horizon
- Risk Identification
- Risk Indicator
- Risk Intelligence
- Risk Interdependency
- Risk Inventory
- Risk Landscape
- Risk Management(RM)
- Risk Management Dashboard
- Risk Management Framework
- Risk Management Maturity
- Risk Management Plan
- Risk Management Policy
- Risk Mapping
- Risk Matrix
- Risk Maturity
- Risk Mitigation
- Risk Mitigation Plan
- Risk Mitigation Strategy
- Risk Model
- Risk Monitoring
- Risk Optimization
- Risk Owner
- Risk Ownership
- Risk Policy
- Risk Portfolio
- Risk Prioritization
- Risk Profile
- Risk Quantification
- Risk Reduction
- Risk Register
- Risk Register Update
- Risk Reporting
- Risk Resilience
- Risk Response
- Risk Response Plan
- Risk Review
- Risk Review Process
- Risk Scenario
- Risk Scenario Analysis
- Risk Scenario Planning
- Risk Scoring
- Risk Sensing
- Risk Sharing
- Risk Strategy
- Risk Taxonomy
- Risk Threshold
- Risk Tolerance
- Risk Tolerance Level
- Risk Transfer
- Risk Transparency
- Risk-Adjusted Return
- Show Remaining Articles (82) Collapse Articles
-
- Business Continuity Risk
- Capital Risk
- Competition Risk
- Compliance Risk
- Counterparty Risk
- Credit Risk
- Credit Spread Risk
- Currency Risk
- Cybersecurity Risk
- Deflation Risk
- Environmental Risk
- Ethical Risk
- Event Risk
- Financial Risk
- Foreign Exchange Risk
- Fraud Risk
- Geopolitical Risk
- Health and Safety Risk
- Human Capital Risk
- Inflation Risk
- Infrastructure Risk
- Innovation Risk
- Insurance Risk
- Intellectual Property Risk
- Interest Rate Risk
- Legal Risk
- Liquidity Risk
- Market Risk
- Model Risk
- Natural Disaster Risk
- Operational Risk
- Outsourcing Risk
- Political Risk
- Product Liability Risk
- Project Risk
- Regulatory Change Risk
- Regulatory Risk
- Reputation Risk
- Reputational Risk
- Resource Risk
- Sovereign Risk
- Strategic Alliance Risk
- Strategic Risk
- Supply Chain Risk
- Sustainability Risk
- Systemic Risk
- Technological Risk
- Technology Risk
- Show Remaining Articles (33) Collapse Articles
-
The SysRisk purchasing process is straightforward—whether you’re buying for a team, an individual, or customizing your plan to fit specific needs. The steps for provisioning a free, paid, or customizable plan are nearly identical. For the free plan, simply provide your card details (you won’t be charged), while for the paid or customizable plans, follow the payment process outlined below.
1. Access SysRisk Pricing Page
To begin, visit https://sysonex.com/sysrisk/.
From the homepage:
- Navigate to the Solutions
- Click on SysRisk – Risk Management.
- Here you will find brief overviews of SysRisk’s offerings.
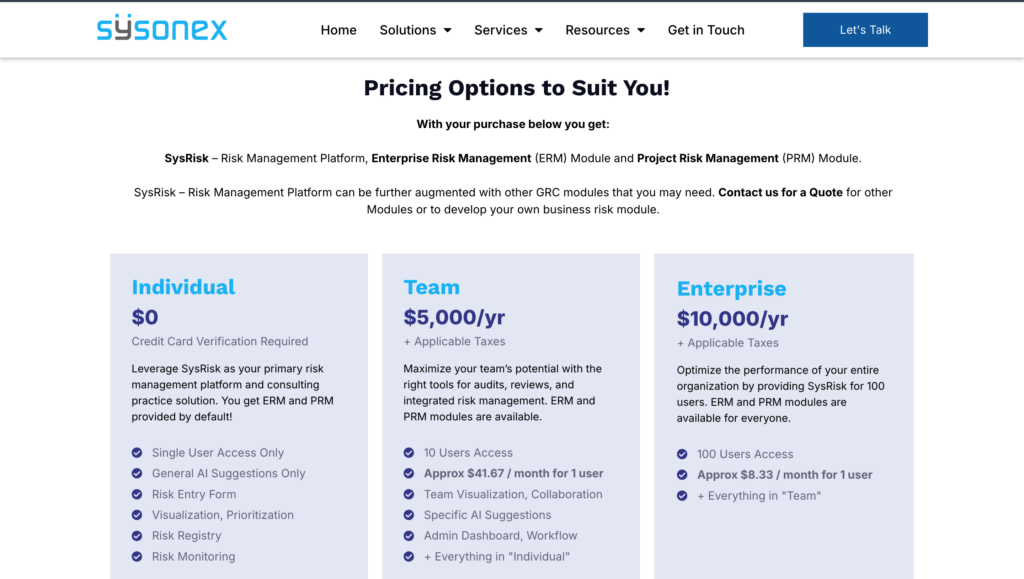
- Scroll down to the Pricing section.
Below the pricing plans, you’ll also find details about customizable facilities.
- Click the action button next to your preferred package to continue.
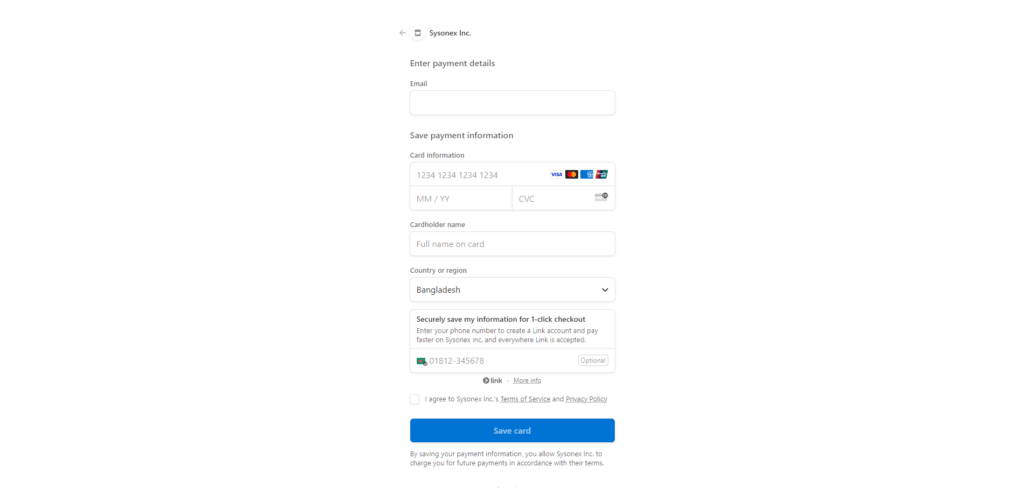
2. Fill in Payment Details
Once redirected, you will see the payment form.
Complete the required fields with your payment information to proceed with the purchase.
With every purchase, you will automatically receive the Enterprise Risk Management (ERM) and Project Risk Management (PRM) modules.
Additional features such as Regulatory Risk Management or Compliance Risk Management can be added separately as paid add-ons.
3. Account Confirmation
After successfully submitting your payment, you will receive an email at your registered email address. This email will include:
- Your account details.
- A login link to access SysRisk.
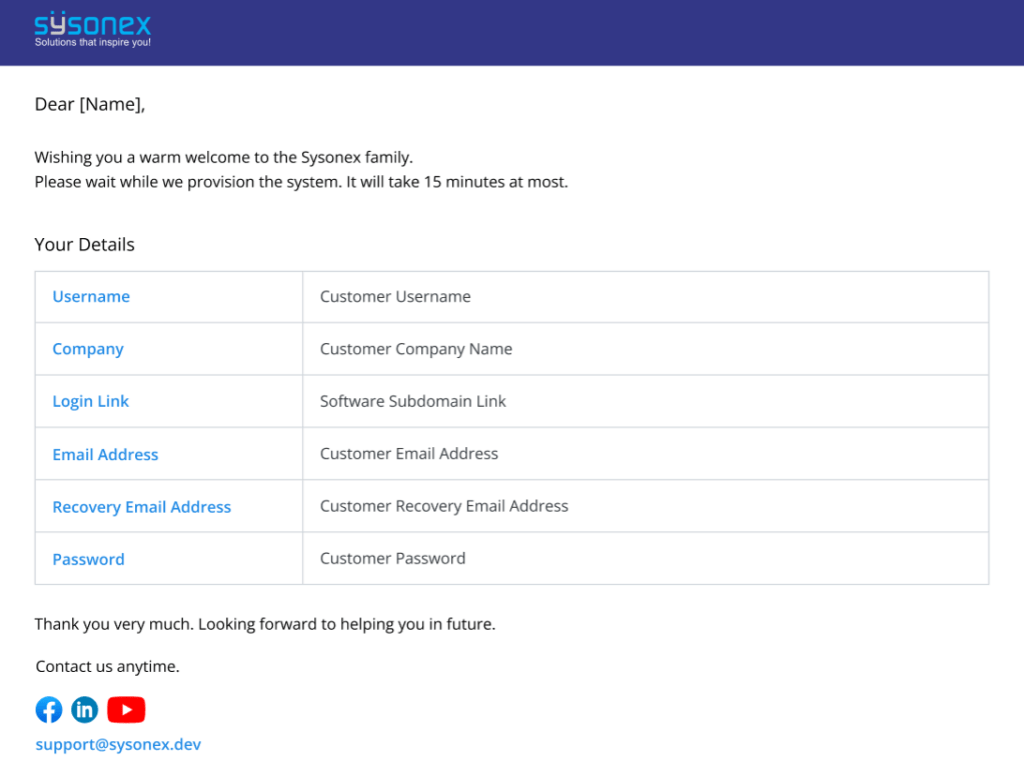
- Click the link to navigate to the SysRisk platform.
4. Login and Setup
– Login using the account details provided in the email.
– Use the temporary password initially sent to you.
– After logging in, be sure to change your password to something more secure for future use.
By following these steps, you can easily complete your SysRisk purchase and begin using the platform. If you encounter any issues during the process, feel free to reach out to SysRisk support for assistance.
