-
FAQs
-
Sysrisk User Manual
-
- Getting Started
- Product Catalogue
- Purchase Process
- Login Process and Forgotten Password Revival Process
- User Creation and Role Assignment
- Customization and Dashboard Configuration
- Project Creation and User Adding Process
- Category Management
- Risk Entry Creation, Edit, and Approval
- Risk Creation Using AI
- Risk Approval Process
- Functionality of Risk Register & Risk Prioritization Page
- Issue creation
- Risk Logs: Administrative and User
- Risk Closure Complete Procedure
- Risk Notification Settings
- Support and Knowledge Base
- Company Profile And AI Risk Creation
- Risk Audit
- Show Remaining Articles (4) Collapse Articles
-
-
Risk Management
-
- Control Risk
- Enterprise Risk Management (ERM)
- Inherent Risk
- Qualitative Risk Analysis
- Quantitative Risk Analysis
- Residual Risk
- Risk Acceptance
- Risk Acceptance Criteria
- Risk Aggregation
- Risk Analysis
- Risk Analysis Methods
- Risk Analytics
- Risk Appetite
- Risk Appetite Framework
- Risk Appetite Statement
- Risk Appetite Statement
- Risk Assessment
- Risk Assessment Matrix
- Risk Assessment Process
- Risk Attribution
- Risk Avoidance
- Risk Bearing Capacity
- Risk Benchmarking
- Risk Capacity
- Risk Capital
- Risk Clustering
- Risk Communication
- Risk Communication Plan
- Risk Concentration
- Risk Contingency
- Risk Contingency Plan
- Risk Control
- Risk Convergence
- Risk Criteria
- Risk Culture
- Risk Dashboard
- Risk Dependency
- Risk Diversification
- Risk Escalation
- Risk Escalation Path
- Risk Evaluation
- Risk Exposure
- Risk Financing
- Risk Framework
- Risk Governance
- Risk Heat Map
- Risk Horizon
- Risk Identification
- Risk Indicator
- Risk Intelligence
- Risk Interdependency
- Risk Inventory
- Risk Landscape
- Risk Management(RM)
- Risk Management Dashboard
- Risk Management Framework
- Risk Management Maturity
- Risk Management Plan
- Risk Management Policy
- Risk Mapping
- Risk Matrix
- Risk Maturity
- Risk Mitigation
- Risk Mitigation Plan
- Risk Mitigation Strategy
- Risk Model
- Risk Monitoring
- Risk Optimization
- Risk Owner
- Risk Ownership
- Risk Policy
- Risk Portfolio
- Risk Prioritization
- Risk Profile
- Risk Quantification
- Risk Reduction
- Risk Register
- Risk Register Update
- Risk Reporting
- Risk Resilience
- Risk Response
- Risk Response Plan
- Risk Review
- Risk Review Process
- Risk Scenario
- Risk Scenario Analysis
- Risk Scenario Planning
- Risk Scoring
- Risk Sensing
- Risk Sharing
- Risk Strategy
- Risk Taxonomy
- Risk Threshold
- Risk Tolerance
- Risk Tolerance Level
- Risk Transfer
- Risk Transparency
- Risk-Adjusted Return
- Show Remaining Articles (83) Collapse Articles
-
- Business Continuity Risk
- Capital Risk
- Competition Risk
- Compliance Risk
- Counterparty Risk
- Credit Risk
- Credit Spread Risk
- Currency Risk
- Cybersecurity Risk
- Cybersecurity Risk
- Deflation Risk
- Environmental Risk
- Environmental Risk
- Ethical Risk
- Event Risk
- Financial Risk
- Foreign Exchange Risk
- Fraud Risk
- Fraud Risk
- Geopolitical Risk
- Health and Safety Risk
- Human Capital Risk
- Inflation Risk
- Inflation Risk
- Infrastructure Risk
- Innovation Risk
- Innovation Risk
- Insurance Risk
- Intellectual Property Risk
- Interest Rate Risk
- Legal Risk
- Liquidity Risk
- Liquidity Risk
- Market Risk
- Model Risk
- Natural Disaster Risk
- Operational Risk
- Operational Risk
- Outsourcing Risk
- Political Risk
- Product Liability Risk
- Project Risk
- Regulatory Change Risk
- Regulatory Risk
- Reputation Risk
- Reputation Risk
- Reputational Risk
- Resource Risk
- Sovereign Risk
- Strategic Alliance Risk
- Strategic Risk
- Strategic Risk
- Supply Chain Risk
- Sustainability Risk
- Systemic Risk
- Technological Risk
- Technology Risk
- Show Remaining Articles (42) Collapse Articles
-
At SysRisk, we are pleased to offer a comprehensive auditing record maintenance facility as part of our services. This dedicated feature allows auditors to generate and manage risk records seamlessly, ensuring data integrity and security. Our platform is designed to support both internal auditors and external auditors hired by the organization, facilitating efficient and reliable auditing processes without the risk of data loss.
Step - By -Step Procedure
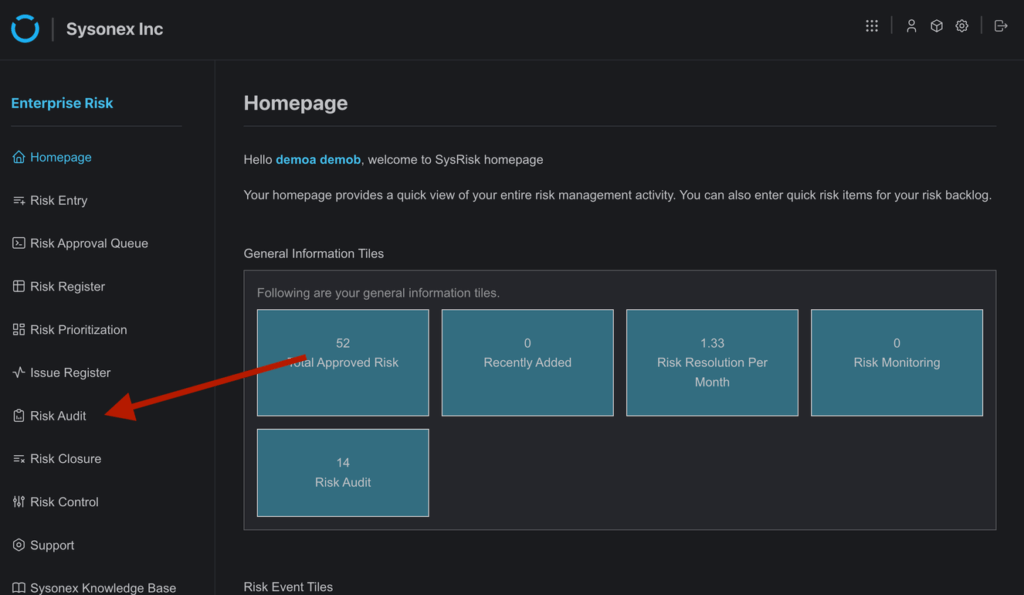
1. Users must first log in and navigate to the homepage of either the ERM (Enterprise Risk Management) or PRM (Project Risk Management) module. From the homepage, users should proceed to the Risk Audit page.
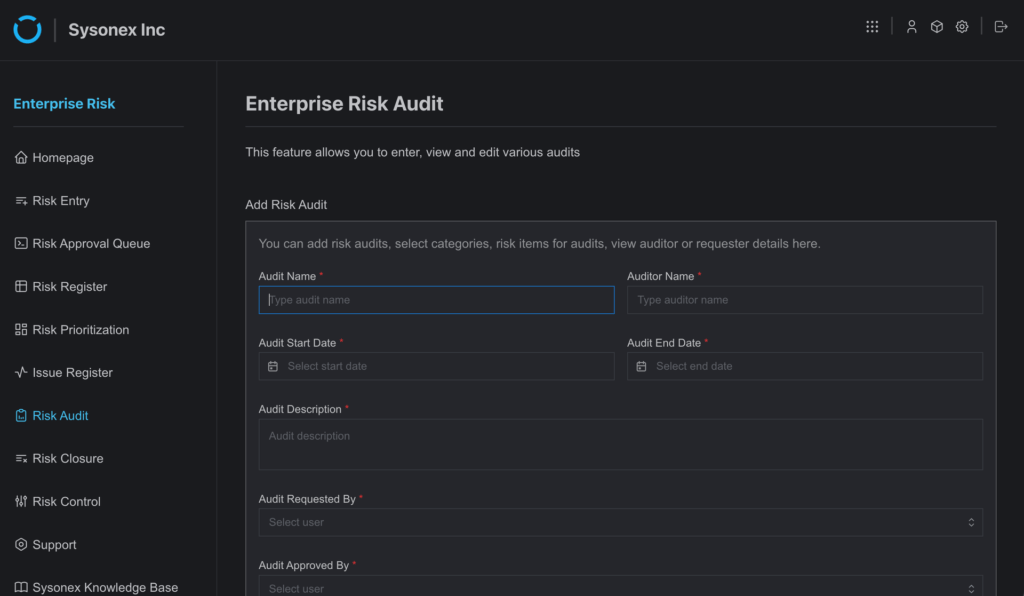
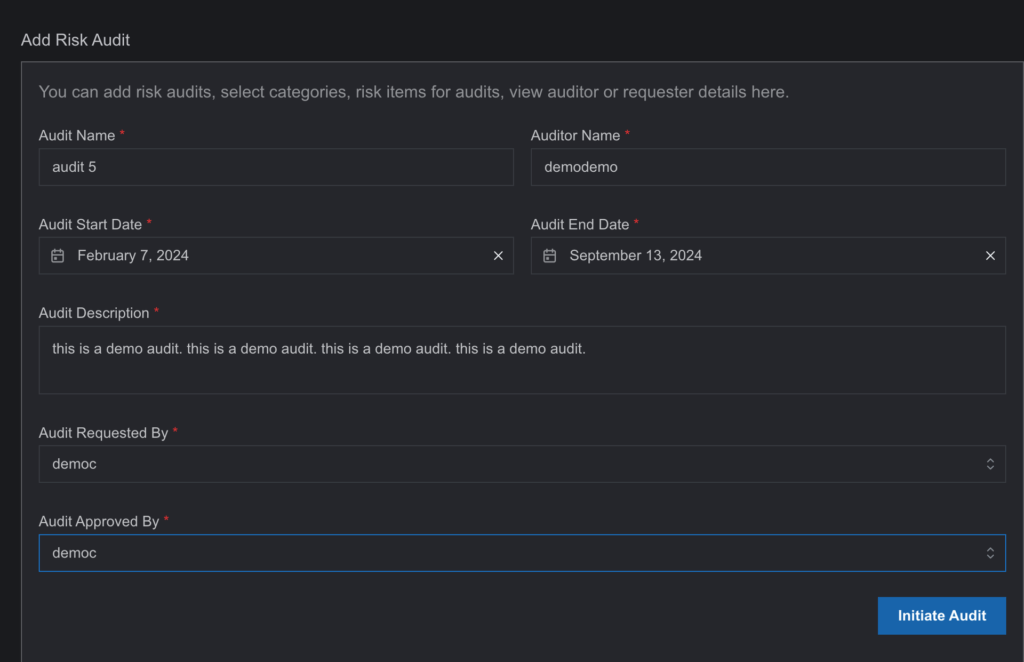
2.On the Risk Audit page, users will find an “Add Risk Audit” form. Complete the form with the required information and select “Initiate Audit.”
3. The newly initiated audit record will appear in the table below the form. Select the “Action” button next to the record to access additional functionalities.
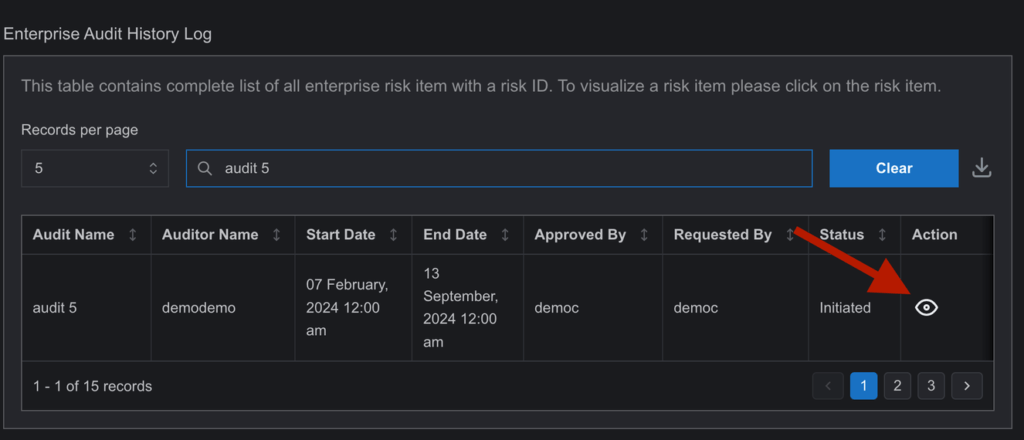
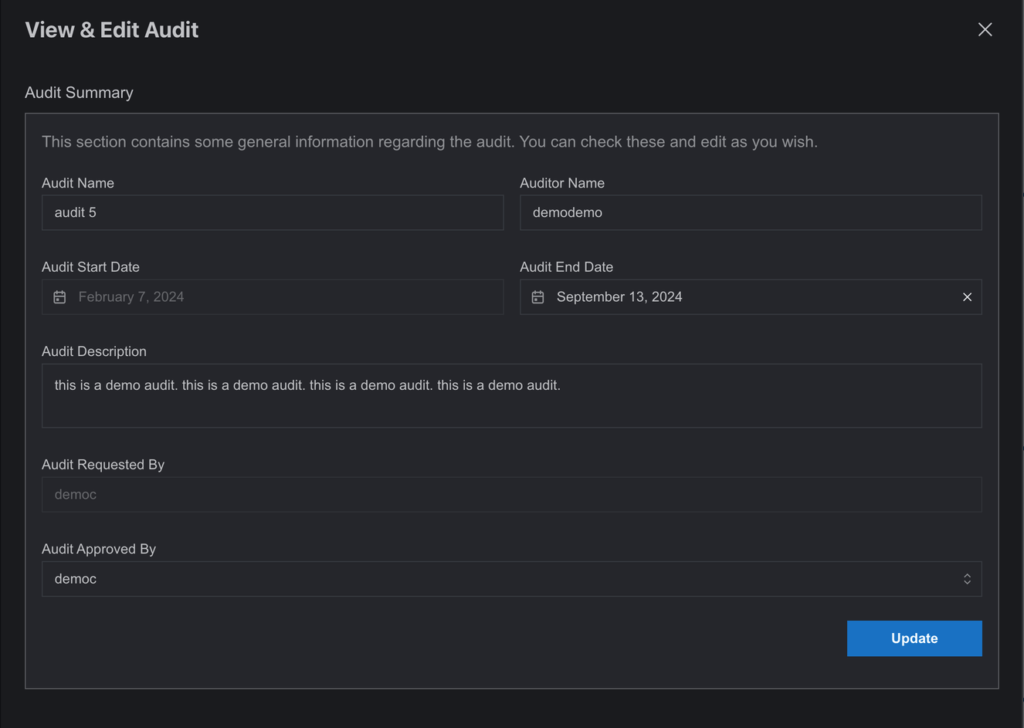
4. The “Action” button will open a subpage titled “View & Edit Audit.” Users can utilize advanced functionalities, including editing previously saved data in the risk audit entry.
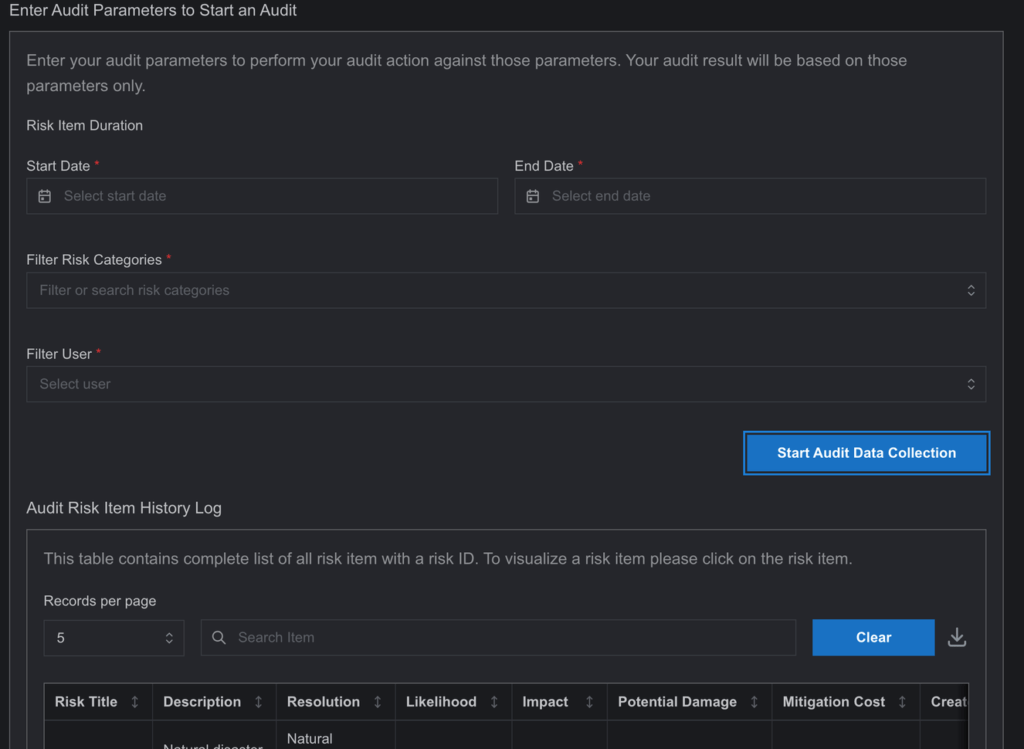
5. Below the “View & Edit Audit” section, users will find a box labeled “Enter Audit Parameters to Start an Audit.” This feature allows users to filter risk entries by date and categories (project for the PRM module) and generate a file in “Audit Risk Item History Log“ table containing the filtered risk entries.
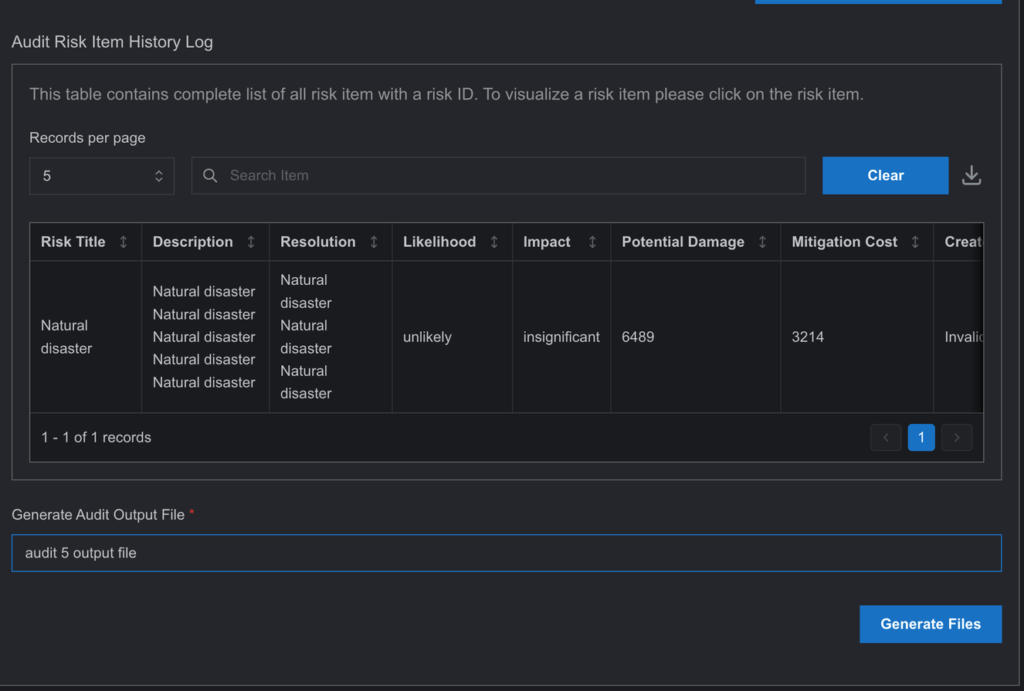
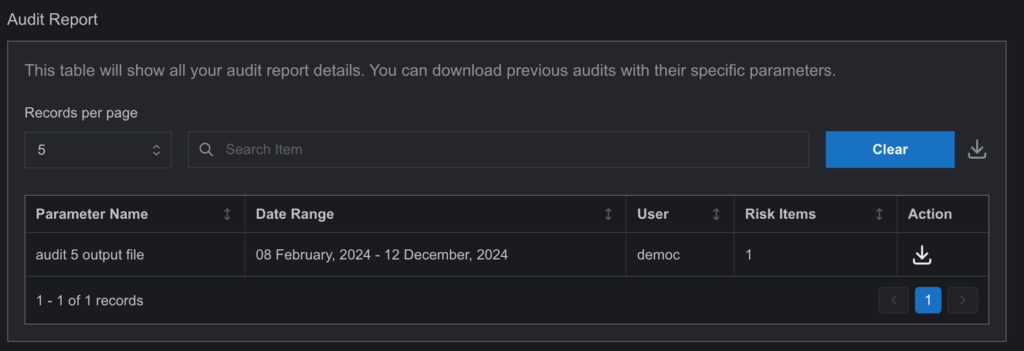
6. The generated file will be uploaded to the “Audit Report” table. Auditors can download the file in CSV or PDF format for their convenience.
By adhering to these steps, users can efficiently manage and maintain their audit records within the SysRisk platform, ensuring a seamless and secure auditing process.
